Blog
Best Self-Hosted Open-Source VPN Solutions
Open-source VPNs have emerged as the most popular option for those who are concerned about their privacy, openness, and complete control over their network infrastructure. With a self-hosted VPN, you don’t have to depend on third-party VPN services, and you have the flexibility to configure your security ...
Domain Portfolio Management Handbook for Businesses
Domain portfolio management is the systematic approach to domain name discovery, registration, protection, organization, valuation, and retirement. It is the process of turning a collection of domain names into a secure and valuable business infrastructure.
Domain portfolio management in a business environment has a direct impact on brand ...
How to set up FileZilla FTP server on Linux easily
The question of How To Set Up FileZilla FTP Server On Linux is a common one among system administrators and developers who require a secure and efficient means of managing file transfers between servers and computers. By properly setting up this particular service, you can effectively manage ...
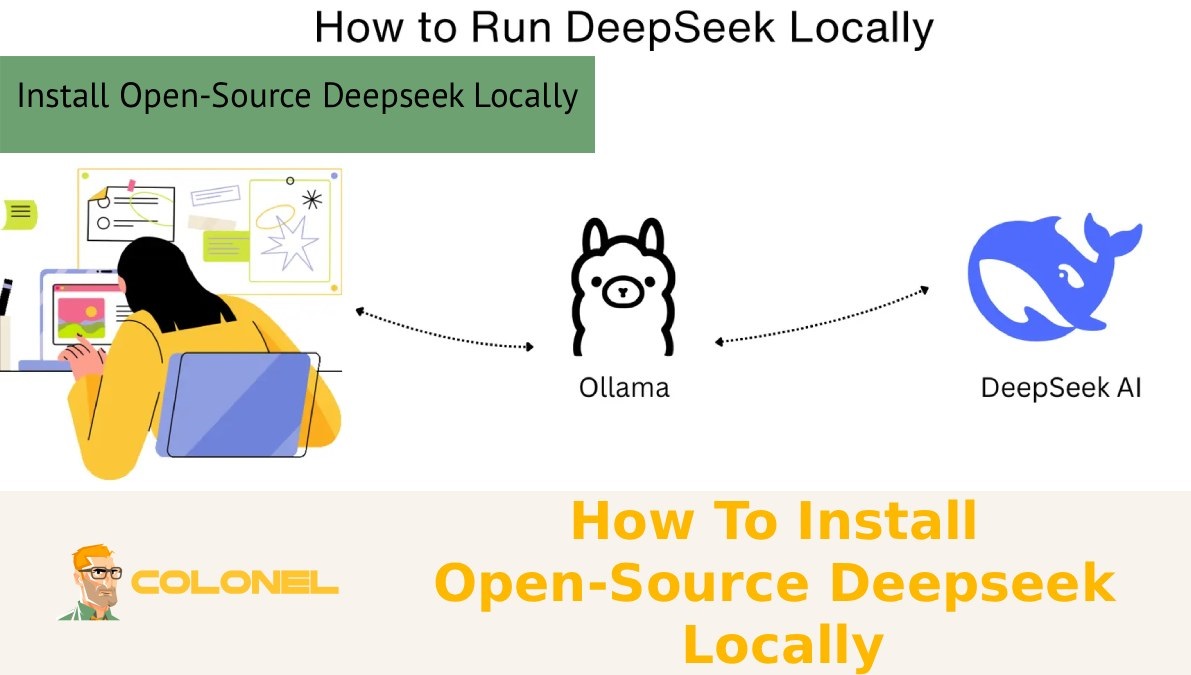
How To Install Open-Source Deepseek Locally
Use Open-Source Deepseek Locally to have complete control over your AI system, improve data privacy, and avoid recurring API fees. With the ability to host your model on your own server, you can personalize performance, optimize resource utilization, and perform advanced inference capabilities without depending on third-party ...
Green Web Hosting: A Comprehensive Guide for Businesses
Green web hosting enables businesses to minimize their digital carbon footprint while maintaining optimal website performance. By leveraging renewable energy, energy-efficient hardware, and carbon offset programs, companies can align their online operations with sustainability goals.
Choosing a verified green hosting provider not only supports environmental responsibility but also ...
How to Set Up a CDN for Faster Websites
How to Set Up a CDN is one of the most effective ways to enhance the speed, reliability, and accessibility of your website. With the help of a CDN, you can distribute your content across various edge servers located across the globe, which helps to reduce latency ...
Stop Email Blacklisting with Smart /24 IP Strategy
Stop Email Blacklisting by using a strategic /24 IP plan that safeguards your sending reputation and ensures that your emails are delivered to the inbox, not the spam box. By spreading your sending volume across a properly warmed IP range, you can avoid triggering spam filters and ...
8 Best FinOps Tools for Cloud Cost Optimization in 2026
FinOps tools for cloud cost optimization are specific platforms that assist businesses in analyzing and optimizing their cloud expenses. As the adoption of cloud services increases on AWS, Azure, and Google Cloud platforms, infrastructure expenses have become difficult to forecast and manage.
The traditional cost management dashboard is ...
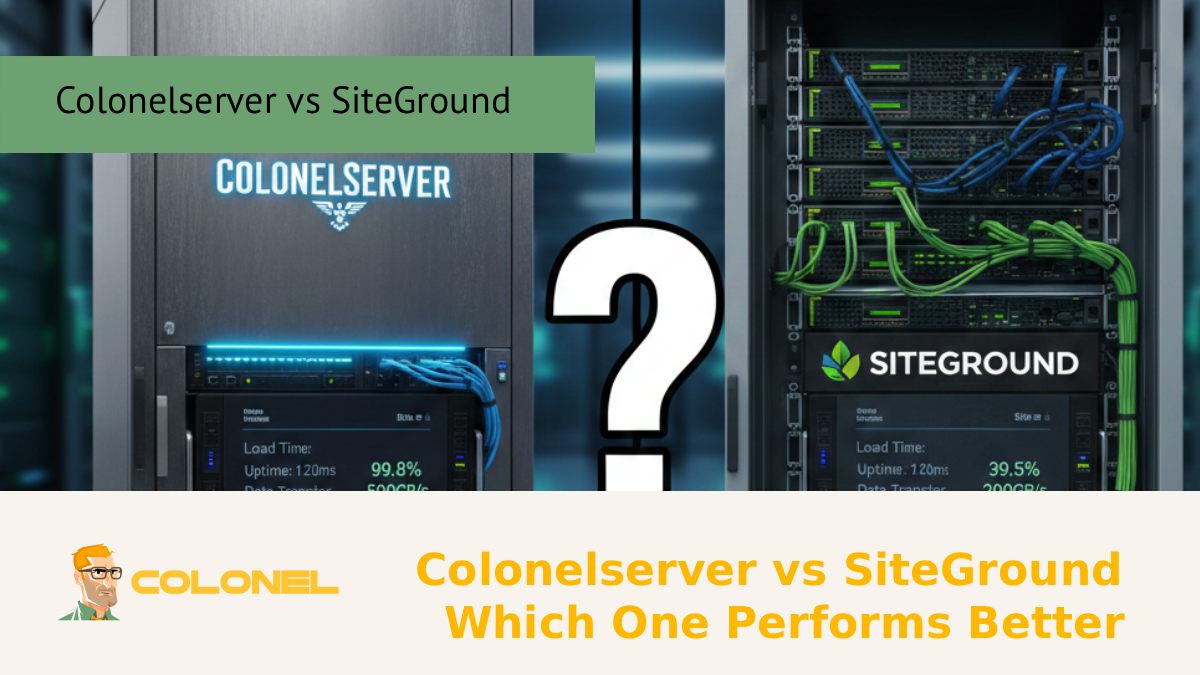
Colonelserver vs SiteGround – Which One Performs Better?
When it comes to performance, a comparison between Colonelserver vs SiteGround reveals that Colonelserver tends to load pages faster and be more reliable when there are a lot of visitors. Although SiteGround is a reputable web host with excellent customer service and reliability, its architecture and resource ...
Container Security Best Practices for Cloud Native and Microservices Architectures
Best practices for container security help safeguard containerized environments against breaches, supply chain attacks, misconfigurations, and runtime threats by integrating security controls throughout the entire lifecycle. With the growing adoption of containers on AWS and other cloud platforms, securing container images, registries, orchestrators, and runtime environments is ...
What is n8n? Workflow Automation for Developers AI
What is n8n? Workflow Automation for Developers AI is a robust open-source platform that helps developers and organizations automate complex tasks without needing extensive coding. Using its node-based graphical interface, n8n helps developers connect apps, APIs, databases, and AI tools together in a smooth workflow, saving time ...
Hackers Actively Exploiting telnetd Vulnerability for Root Access
A critical security flaw in the GNU InetUtils telnetd server (CVE-2026-24061) is being actively exploited by attackers worldwide. The telnetd vulnerability allows unauthenticated attackers to bypass standard login procedures and gain root access on affected Linux systems. Researchers have observed coordinated campaigns targeting the Telnet service, highlighting ...
AI Load Balancing for VPS Hosting: Intelligent Resource Management
AI load balancing for VPS hosting is a machine learning-based traffic routing solution that automatically directs traffic to VPS nodes based on performance data. In today’s VPS hosting setup, where traffic patterns are constantly fluctuating and workloads are diverse, AI load balancing replaces rigid traffic routing logic ...
How to Start a Online Business in 2026?
How to Start an Online Business is a query that many individuals are faced with when they have ideas, skills, or products that they wish to monetize on the internet. With the ever-increasing popularity of digital platforms, starting an online business has become easier than it was ...